From Web App Security to Physical Security: A Holistic Approach to Network Management
Today, network security has become more complex and critical than ever before. With the increasing frequency and sophistication of cyber threats, organizations must ensure that all security framework components are robust and well-integrated. From Web App Security to Physical Security: A Holistic Approach to Network Management emphasizes the importance of addressing digital vulnerabilities and physical security concerns. By integrating these various aspects into a unified strategy, organizations can achieve comprehensive protection against diverse threats, ensuring their digital and physical infrastructures are secure.
A unified security strategy is essential, as vulnerabilities in one area can significantly impact others. For example, a breach in web application security can expose network and physical systems to attacks, underscoring the need for an integrated approach. Organizations can better manage risks and safeguard assets by understanding and implementing a holistic security approach.
Understanding Network Security Components
Web App Security
Web app security focuses on protecting online applications from various cyber threats. This includes safeguarding against attacks such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). Web applications are often targeted due to their direct interaction with users and their role in handling sensitive data.
Best Practices:
- Secure Coding: Implement secure coding practices to mitigate common vulnerabilities.
- Regular Updates: Ensure web applications are regularly updated to patch known vulnerabilities.
- Vulnerability Assessments: Conduct periodic assessments to identify and address security weaknesses.
Physical Security
Physical security involves protecting hardware and facilities from unauthorized access and damage. This aspect of security is crucial, as physical breaches can lead to significant data loss and operational disruptions.
Common Threats:
- Unauthorized Access: Risks such as theft or tampering with physical devices.
- Physical Damage: Natural disasters or vandalism.
Best Practices:
- Surveillance: Use cameras and monitoring systems to deter and detect unauthorized access.
- Access Controls: Implement strict access control measures to restrict entry to sensitive areas.
- Environmental Controls: Protect against environmental threats like fire and flooding with appropriate safeguards.
According to IFSEC Insider, 2023, physical security incidents cost companies approximately one trillion US Dollars in 2022 (IFSEC Insider)
Read More About Best Practices
Network Security
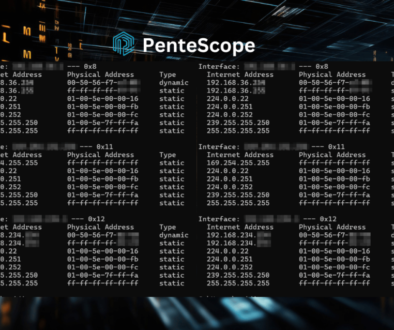
Network security is vital for safeguarding data during transmission across networks. It involves protecting against malware, phishing attacks, and Distributed Denial of Service (DDoS) attacks.
Best Practices:
- Firewalls: Use firewalls to filter incoming and outgoing network traffic.
- Intrusion Detection Systems (IDS): Implement IDS to detect and respond to suspicious activities.
- Encryption: Protect data in transit with strong encryption protocols.
A 2023 report by IBM Security found that companies with robust network security measures experienced significantly faster breach detection and containment times than those with weaker defenses.
Integrating Security Measures
Synergizing Web App and Network Security
Web applications and network security are deeply interconnected. Vulnerabilities in web apps can compromise network security, leading to more extensive breaches.
Unified Strategies:
- Cross-Protection Measures: Implement security measures that simultaneously address web apps and network infrastructure vulnerabilities.
- Case Studies: In the 2021 SolarWinds attack, for instance, attackers exploited vulnerabilities in network monitoring tools to compromise web applications and access sensitive data.
Benefits: A unified approach enhances overall protection and simplifies management by addressing interconnected threats comprehensively.
Combining Physical and Network Security
Integrating physical and network security can prevent breaches that target physical access and network systems.
Converged Security:
- Securing Server Rooms: Physical security measures, such as access controls and surveillance, support network security by protecting server rooms and data centers.
- Case Studies: In the 2019 Capital One breach, attackers exploited physical security weaknesses to access sensitive data stored in a compromised network.
Benefits: This approach improves incident response and reduces the risk of multi-layered attacks.
Challenges and Solutions in Integration
Common Challenges:
- Compatibility Issues: Different security systems may not always integrate seamlessly.
- Resource Constraints: Integrating various security measures can strain organizational resources.
Solutions:
- Cross-Training Teams: Train security teams across all areas to effectively manage and respond to integrated security threats.
- Integrated Security Platforms: Use comprehensive solutions for web apps, networks, and physical security.
Best Practices for a Holistic Security Approach
Developing an Integrated Security Policy
Policy Creation:
- Comprehensive Policies: Develop policies that address all security aspects—web app, network, and physical.
- Best Practices: Include guidelines for regular updates, monitoring, and enforcement.
Implementing Cross-Disciplinary Training
Training Importance:
- Holistic Training: Provide web apps, networks, and physical security training.
- Program Examples: Successful programs, like those implemented by companies such as Google, have led to improved security posture and faster incident response.
Utilizing Advanced Security Technologies
Technology Overview:
- Unified Threat Management (UTM) Systems: Combine various security features into a single platform.
- Security Information and Event Management (SIEM): Provide real-time monitoring and analysis of security events.
Future Trends and Innovations
Emerging Security Technologies
Innovations:
- AI-Driven Security Analytics: Utilize artificial intelligence to enhance threat detection and response.
- IoT Security Solutions: Address vulnerabilities in connected devices.
Evolving Threat Landscapes
Future Threats:
- Predicted Threats: Expect increased threats from advanced persistent threats (APTs) and sophisticated phishing attacks.
- Preparation: Implement adaptive security strategies to stay ahead of evolving threats.
Recommendations for Future Security Strategies
Adapting Strategies:
- Integration of Emerging Technologies: Continuously incorporate new technologies into existing security frameworks.
- Continuous Improvement: Regularly evaluate and update security measures to address new vulnerabilities.
Practical Recommendations
Creating a Comprehensive Security Plan
Plan Development:
- Holistic Plan: Develop a plan that covers web apps, networks, and physical security.
- Policy Enforcement: Ensure the plan is enforced across the organization to maintain consistent security practices.
Investing in Integrated Security Solutions
Solution Selection:
- Criteria: Choose solutions that offer integration across different security layers.
- Best Practices: Effectively use these solutions to enhance overall security.
Ongoing Monitoring and Evaluation
Continuous Monitoring:
- Importance: Regularly monitor and evaluate security measures to adapt to new threats.
- Staying Informed: Keep up with the latest security trends and advancements.
Conclusion
In today’s interconnected digital landscape, securing your organization requires more than isolated efforts—it demands a unified, holistic approach. By integrating web application security, network protection, and physical safeguards into a cohesive strategy, businesses can effectively defend against evolving threats. This alignment fortifies critical infrastructure and ensures that vulnerabilities in one area do not compromise the entire system.
From advanced technologies like AI-driven analytics to practical measures like cross-disciplinary training, the path to robust security involves innovation, adaptability, and consistent vigilance. As highlighted, organizations that embrace integrated security strategies experience fewer breaches and faster response times, reinforcing the value of a comprehensive approach.
Ultimately, safeguarding your organization’s assets isn’t just about addressing current vulnerabilities—it’s about anticipating future risks and proactively adapting to an ever-changing threat landscape. By prioritizing a holistic security framework, your organization can achieve resilience, protect critical assets, and inspire trust in a world where security is non-negotiable.
Call to Action
We invite you to subscribe to our monthly newsletter and follow us on our Facebook, X, and Pinterest channels for more insights and updates on cybersecurity trends and best practices. Our blog provides valuable information and resources to help you stay informed and prepared against evolving threats.
Engage with our community to share knowledge, ask questions, and stay connected with industry developments. Visit our About Us page to learn more about who we are and what we do. If you have any questions, please reach out through our contact page. You can also explore our services to discover how we can help enhance your security posture.
Frequently Asked Questions
A holistic security approach integrates multiple security layers, including web app, network, and physical security, to provide comprehensive protection against various threats.
Integrating physical and network security helps ensure that vulnerabilities in one area do not compromise the other, enhancing overall protection and response capabilities.
Challenges include compatibility issues, resource constraints, and managing multiple security layers effectively.
Technologies like AI-driven analytics and unified security platforms can streamline and enhance the integration of various security measures, providing better protection and efficiency.
A comprehensive security plan should address web app, network, and physical security, include clear policies, and outline procedures for regular monitoring, updates, and response to threats.