Cybersecurity Insights & News
Expert knowledge and real-world guidance to help you stay safe in the digital world.
What is Bluejacking and Bluesnarfing? Understanding Bluetooth Security Threats
Bluetooth technology has changed the way we connect our devices, providing convenience and seamless communication. However, hidden within this wireless […]

SSL Stripping Attacks: How They Work and How to Prevent Them
Imagine you’re shopping online, ready to buy something you’ve had your eye on. You enter your credit card details, hit […]
What is Network access control Bypass?
Network Access Control (NAC) systems are designed to be the vigilant gatekeepers of our digital fortresses, safeguarding our networks from […]

Learn ARP Cache Poisoning in 10 Minutes
Have you ever wondered how hackers can sneak into networks undetected? ARP Cache Poisoning – a stealthy technique that can […]

What is MAC Address Spoofing?
Have you ever felt like your online identity is an open book? In a world where digital footprints are becoming […]
How to Prevent Pass-the-Hash Attacks: Steps and Tools
Imagine a cyber attacker silently moving through your network, accessing sensitive data without cracking a single password. This nightmare scenario […]
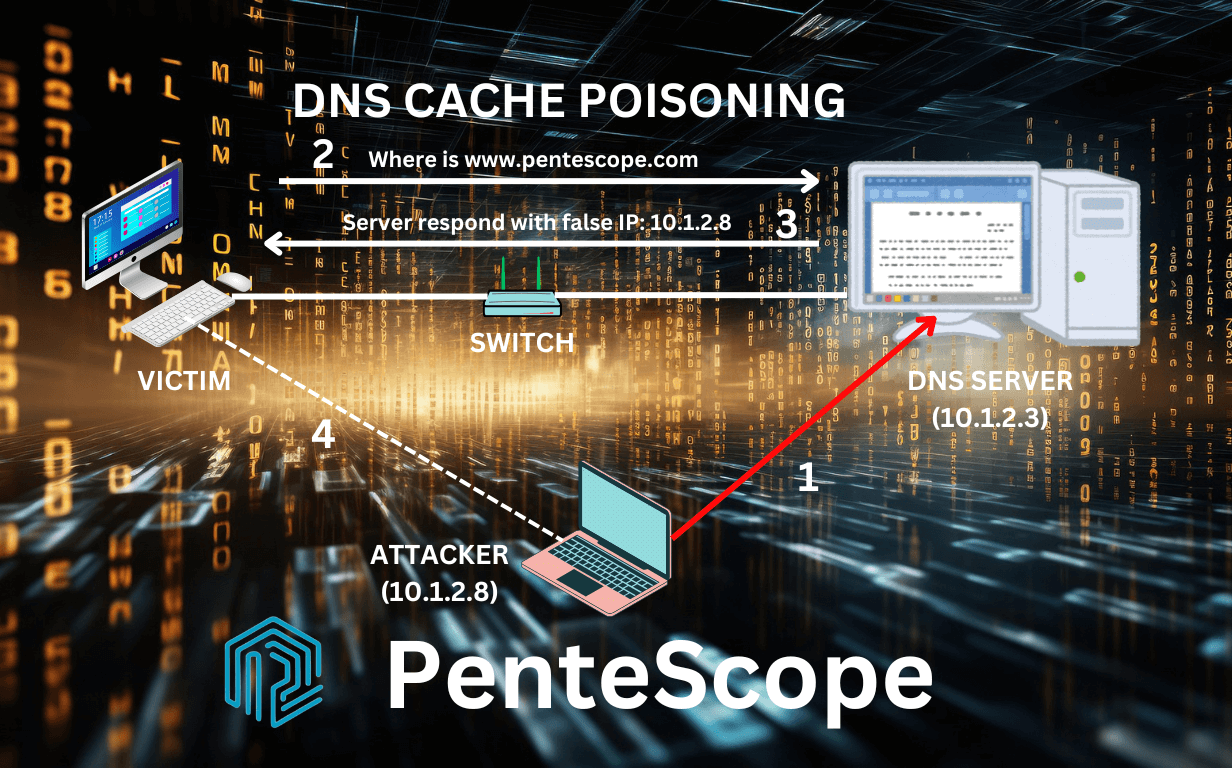
What is DNS Cache Poisoning?
Imagine browsing the web, confident in your online security, only to find yourself on a malicious website masquerading as your […]

Steps to Land Your First Penetration Testing Job
Have you ever dreamed of becoming a professional penetration tester—the kind that helps organizations strengthen their cybersecurity? If so, you’re […]

Everyday Cybersecurity Challenges: How to Stay Safe Online
Are you constantly worried about your online safety? You’re not alone. In today’s interconnected world, the internet has become an […]
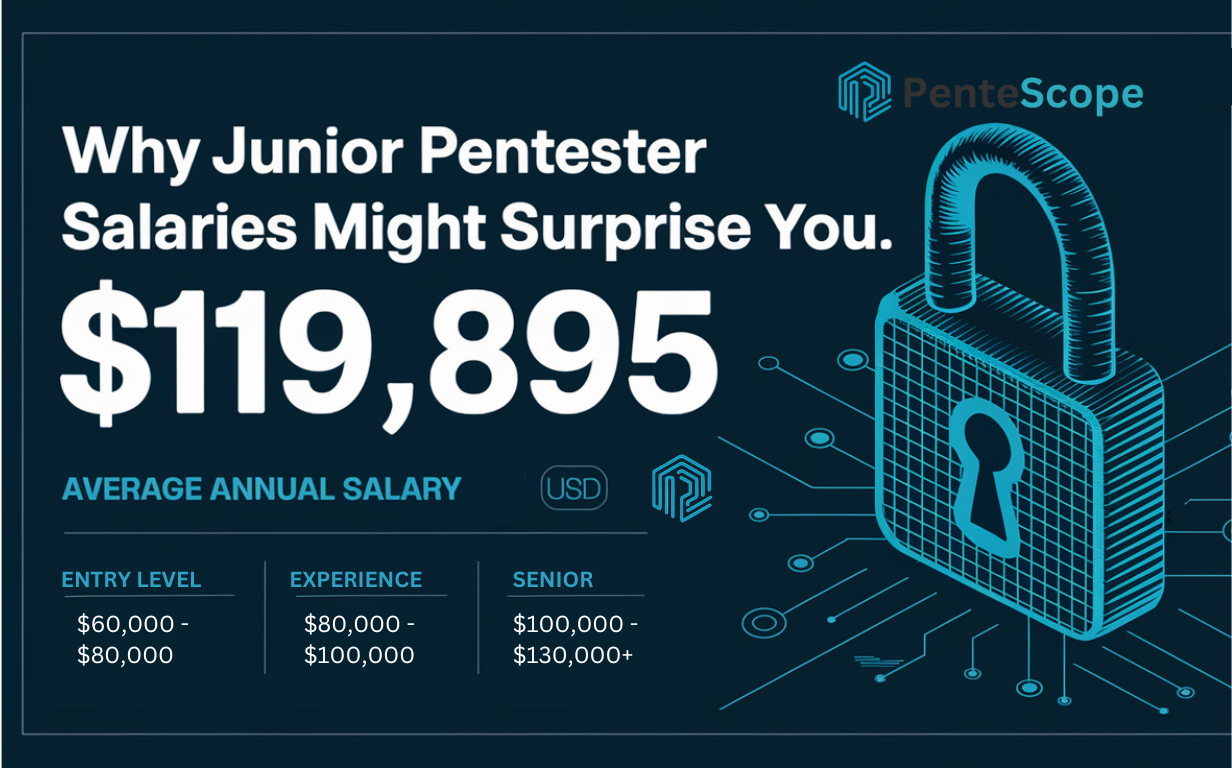
Why Junior Pentester Salaries Might Surprise You
Attention, aspiring cybersecurity professionals! Are you considering a career as a junior penetration tester? Prepare to be astonished by the […]

Ransomware Attacks: The Alarming Rise and How to Protect Yourself
Imagine waking up one day to find all your digital files locked, your personal information held hostage, and a menacing […]

Clickjacking and Phishing: What’s the Difference?
In an era where digital security threats lurk around every corner, two terms often surface in discussions about online safety: […]

Flipper Zero Attacks: How to Safeguard Your Systems from Exploits

Types of Vulnerability Scans and Scanners: Comprehensive Guide to Tools and Best Practices

How to Identify Social Engineering Attacks in Your Organization

Ethical Challenges in AI-based Penetration Testing: Key Insights
Cybersecurity Insights FAQs
What topics does the PenteScope blog cover?
We cover penetration testing, offensive security, threat intelligence, digital safety tips, and cybersecurity trends.
How often do you publish new content?
Who writes your blog posts?
Can I contribute a guest post?
How can I stay updated on new posts?
Are your articles beginner-friendly?
Do you cover breaking cybersecurity news?
